Table of Contents
Many organisations are already using cloud solutions with great success. But how secure will this new environment be? Will you be able to keep up with legislative requirements or compliance commitments?
The short answer is yes, but with a few caveats – namely implementation, future-proofing, and adequate skills.
Here at Experteq, we have chosen Microsoft as our partner of choice, using Azure’s cloud platform to meet various organisational needs. On top of selecting the right cloud platform, partnering with a managed service provider will allow you to further offload your governance and compliance requirements.
Security built in
When designing a cloud solution, providers try to architect a solution which will meet the needs of a vast and diverse range of clients. Microsoft adopted a Well-Architected Framework principle. One of the core tenets of Well-Architected Framework is Security and includes the following:
However, there are other points which are worth mentioning:
Azure cloud uses a “Zero Trust” principle
It moves away from end user perimeter-based security, and assumes any endpoint has the potential to be hostile. This has prompted the following fundamentals:
Verify explicitly: Always authenticate and authorise on all available “data points” including identity, location, device health, service/workload data classification.
Use least privilege: Limit user access with just-in-time and just-enough-access (JIT/JEA), risk-based adaptive polices, and data protection to help secure both data and productivity.
Assume breach: Minimise containment areas and segment access. Verify end-to-end encryption and use analytics for visibility, to drive threat detection and improve defences.
It provides robust protection and storage of information
Data sovereignty means your data resides in the geopolitical zone of your choice. Your data will never leave the data centres of your country. Services like key vaults allow cryptographic keys and secrets to be protected and accessed on your terms.
It leverages a global team of security professionals
By using Azure you are benefiting from a team of more than 3,500 global cybersecurity experts. These professionals work together to shape the tools and services available in the cloud, thus enabling you to better safeguard your assets.
Simpler, more intuitive management
As your infrastructure grows, so does the hassle of security and monitoring of multiple assets. Luckily you have access to a growing list of features to support your growth.
More importantly, through “a single pane of glass” – i.e. by consolidating data from multiple sources into one display – all these capabilities are available instantly, and assets can be onboarded with minimal effort.
Microsoft Sentinel: A one-stop shop for attack detection, threat visibility, proactive hunting, and threat response in a security information and event management (SIEM) and security orchestration, automation, and response (SOAR) solution.
Defender for Cloud: Integrated security monitoring and policy management that helps you detect threats that might otherwise go unnoticed.
Azure Monitor: A useful tool for forensic and other security analysis, you will be able to quickly search through large amounts of security-related entries.
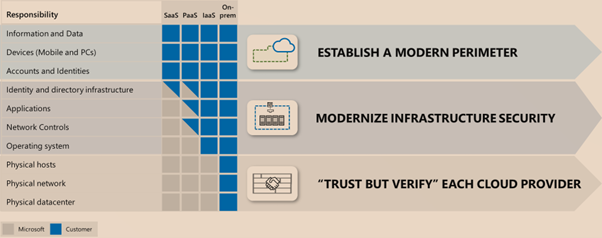
Shared responsibility for compliance
With the cloud, you share your responsibility when it comes to meeting legal and regulatory standards. The hassle of meeting certain requirements can be mitigated based on the level of services you consume.
Many compliance standards have overlapping controls. Fortunately, cloud operators handle much of the heavy lifting, mapping these controls and standards to their environment so you don’t have to.
The majority of our financial services clients are content knowing Azure complies to standards and organisations like PCI DSS, APRA and ISO. You can find more information here.
Achieving an easier, smoother and more secure cloud transition
While the move to cloud can be a daunting prospect, cloud providers are working hard to make the process simpler and easier. However, there are a number of risk areas that need to be highlighted.
Simple doesn’t always mean secure. Mistakes, misconfigurations and flawed internal processes could mean a backdoor for a malicious attacker.
The problem is not the cloud solution, but who you engage to perform your implementation. An organisation with a history of diverse implementations, a strong security team and the correct skill set is crucial for a successful ongoing relationship with a cloud environment.